An Overview Of Internet Security Basics You Should Know
Here’s a brief overview of the Internet Security Topics that are most concerning today.

Phishing
When you cast a fishing line into a lake you’re hoping to catch the eye of a fish gullible enough to believe whatever you bait your hook with is an actual meal. Once you feel the tiniest nibble you give your fishing pole a quick tug to secure your catch. You’ll probably have to throw your line out many times before you catch anything but it’s a numbers game. You know from experience the fish are out there waiting to become your next meal.
The same principles apply to phishing emails. They look very realistic and try to make it seem like there’s a problem with one of your online accounts when there isn’t. If you do what they ask you’re giving the bad guys your personal information and passwords. It’s not difficult to copy the HTML code and formatting from a legit email and create a bogus one. The only discernable difference will be the links. If you hover your mouse over the links and email address in the body of the email you should be able to tell which ones are real and which ones are fake.
No time to read right now? Download this article in convenient PDF format.
If you hover your email over a legitimate email address or link it will usually make sense. A bogus email will contain spelling errors or will be randomly generated and sometimes contain weird characters. Stay away from these. It’s best to just delete them to avoid the temptation to click on them.

Legit email address

Bogus randomly generated email address
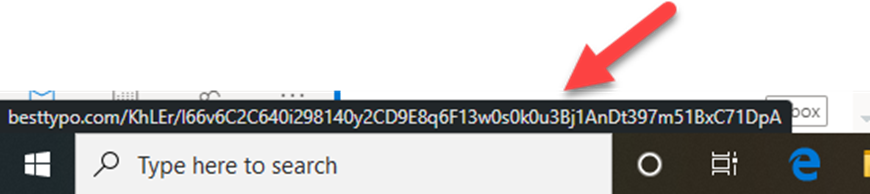
Hovering your mouse over the link in the email message above displays another randomly generated address in the bottom left corner of the window. This email message has “delete” written all over it.
You may receive a realistic-looking phishing email that says your account is overdrawn or there’s some other problem. If you find yourself concerned about the actual status of that account go to the website directly without using the links in the email.
Once a hacker captures your email address and password on his site can try that email/password combination on multiple accounts because many people use the same password and password combination on multiple sites. Even if you don’t provide a password he can use your email address as the “reply to” address on spam emails and make it look like you’re the one doing the spamming.
Ransomware
The Crypto-Locker virus example I used in this chapter is a perfect example of ransomware. Your ability to use your computer or access your data is disabled and literally “held for ransom” until you pay up.
Even though ransomware infections have been around a long time they are still effective. A common type of ransomware was known as a “Fake AV.” A pop-up would announce your antivirus software needed to be updated. If you clicked on it you would download something that looked like an antivirus program along with a ton of malware to your computer. Next, you would see all sorts of error messages and notifications claiming the problems can be removed for a fee. If you paid the fee it would work for a short time and then start up again.
Unfortunately, the fact that there is money to be made has encouraged cyber-criminals to become more and more clever. As a result, ransomware is becoming more sophisticated and more prevalent. Some ransomware infections even can disable your antivirus. Ransomware issues don’t go away easily. Many times the only way to permanently get rid of them is to format your hard drive and reinstall your operating system and programs from scratch. This is why backups are so important.
The best ways to avoid ransomware infections are:
- Avoid downloading anything from less than reputable sites.
- Hang up on phone calls from anyone claiming there’s a problem with your computer and they can fix it. Don’t even engage them. If possible don’t even answer your phone if it’s a number you don’t recognize.
- Avoid clicking on attachments in emails from unknown senders or weirdly formatted email addresses. (See Phishing)
Passwords
Let’s face it these days almost everything of value is protected by little more than a flimsy string of numbers and letters called a “password.” It’s a scary thought. It’s also an opportunity to separate yourself from the low-hanging fruit with a strong, complex password.
It’s a simple thing. The longer and more complex the better. Unfortunately, the more difficult passwords are to crack the more difficult they are to remember. That’s why password managers like Lastpass and Bitwarden and so useful. They’re extremely easy to set up and use.
One “Master Password” will give you access to the usernames and passwords of all the sites you frequent. Some password managers will even generate a complex password for you. Of course, you’ll need to go through the pain of manually changing the passwords on those accounts but once that’s done the rest is gravy.
In addition to using a password manager, I have all my most important passwords in a text file that I keep in a secure location. If you don’t want to deal with the learning curve of some new-fangled password generator and prefer to create your passwords here are a few rules of thumb.
- Don’t use personal information such as your name, phone number, pet’s name, or street name in a password. You’re just making it easy for hackers with information about you. Entering everything they know about you into a “Rainbow table” can dramatically reduce the number of possible passwords a brute force attack has to attempt.
- If you insist on human-sounding passwords replace some of the letters with numbers and vice versa. Using this technique “momsapplepie” becomes “m0m5appl3p1e”
- Use capital letters, numbers, and special characters to make a password even stronger. For example: M0m5appl3p1e!?1” The trailing “!?1” is easy to remember and can be used to add complexity to multiple different passwords.
- Websites drop all kinds of junk in on your computer to collect marketing information on you all the time. Hackers can also extract passwords saved in your browser. That’s why I no longer save passwords in my browser.

Just say no.
Here’s a site that’s kind of fun and illustrates how strong your password is. It uses special algorithms to estimate how much time it would take for a brute force attack to crack your password. Simply type in your password and hit Enter.

In the example above I just typed in a bunch of random characters without looking. This illustrates how effective a nonsensical string of random characters can be. Here is an example of a 16-character password generated by passwordsgenerator.net: ^:d`P$46D`2b3Lu,
Entering that into the password strength test site mentioned above produced a result of “4 thousand trillion years.” That’s enough to ruin any hacker’s day.
Drive-By Downloads
Don’t worry, I’m not getting ready to tell you, “Don’t visit junk download sites and download tons of files with malicious software on them.” You already know that. “Drive-by Download” sites are much more sophisticated and insidious than knowingly downloading risky software programs onto your computer.
Like many, you may feel the most annoying thing about computers is the constant updates. I mean why can’t they get it right the first time right? Well, there are very good reasons for all those updates. There are people out there who have nothing better to do than scrub through popular software programs and operating systems to find vulnerabilities they can exploit.
A recent Java exploit was so bad it could be used to take complete control of a computer. The US government stepped in and told people to uninstall Java from their computers until Java was able to fix the vulnerability. Even though Java quickly patched the vulnerability the use of Java is gradually being phased out on most browsers.
These vulnerabilities are like gold to hackers and can be sold or rented to other hackers with the expertise and motivation to deploy them. Those vulnerabilities are then loaded into “Drive-by Download” sites which check each computer for outdated software programs that will likely be vulnerable to various exploits. The site then infects each computer with the exploits it’s most vulnerable to.
Sinister yet ingenious.
The most popular way to get people to visit these “Drive-by Download” sites is with the use of phishing emails that appear to be from someone on the victim’s email contacts list saying, “Hey, check this out!” The victim is unwittingly led to a perfectly normal-looking site that is secretly loading exploits that are tailor-made for his system.
Another reason to double-check emails for links to unknown sites.
The best way to avoid the impact of “Drive-by Download” sites is simple. Always keep your software programs and computer operating system updated. Just Do It!
Email Attachments
The most popular way to infect computers is still with the use of email attachments. We all like sending pictures and links to cool sites to our friends. This can lead to impulsively clicking on links and attachments out of sheer curiosity. If you do get an email with an attachment make sure:
1. It’s from someone you know.
2. The extension of the file is .jpeg, .jpg,.gif, or some other image format. Avoid clicking on attachments with .zip or .exe extensions. Those are “executables” and can be used to run programs and malware.
Microsoft Excel and Word files have been known to contain macros that can contain malicious code but these are usually detected and handled with a good antivirus software program. There are exceptions to every rule so things can get confusing. The best rule of thumb to follow is to never open an attachment from someone you don’t know – period.
Multi-Factor Authentication
Back in the day phones were ugly boxes, with tangled-up cords hanging on the wall. They made a horrible noise when someone wanted to reach you and they hurt your fingers when you tried to dial out. Now they are pocket-sized computer systems that provide us all a private window to each other and the world.
Phones – are we becoming too reliant on them? It’s too early to say. For now, they can do just about everything but the dishes. Our reliance on the internet has led to our most important internet assets being a simple username and password away at all times. Unfortunately, that means they’re a simple username and password away from the bad guys as well.
So what happens if somehow someone gets access to our most important usernames and passwords? They can turn our worlds upside down until we manage to change our passwords or disable our accounts. This is where multi-factor authentication comes in.

With multi-factor authentication, the correct username and password aren’t enough. You also must have a phone and website that sends that phone a special code. You add that one-time-use-only code to your website credentials and if you get everything right you’re in.
Simple right? Not really. It’s kind of a pain but if nothing like the pain of unauthorized access to your most important accounts. It’s becoming more and more commonplace for major internet sites to offer multi-factor authentication. I suggest looking into it and trying it on a few accounts to get the hang of it. Some day it may be mandatory. It’s a very secure and effective method of security – until you lose your phone or your battery dies that is.
That brings me to my original question: Phones – are we becoming too reliant on them? Time will tell I guess. In the meantime, we might as well make the best the best possible use of everything technology has to offer us. It’s been a great ride so far and it will probably only get better!







