One Of The Scariest Days Of My Life
A website on how to set up an Awesome Home Network wouldn’t be complete without a section on how to protect it. I’d be shirking my responsibilities as the author if I didn’t include some information on Antivirus and Internet Security. Especially after the experience, I had while working on my Home IT Handbook.

In this chapter, I’ll describe the harrowing experience I had with a hacker, how I left myself open, how I recovered from it, and what I did to protect myself from it happening again. Hopefully, you’ll be able to learn from my mistakes and never have to go through the same thing yourself.
A Nightmare Come True
One beautiful Saturday morning I sat down at a test computer I was preparing to use for “Chapter 13 – Remote Control” of my eBook and there was a threatening-looking webpage staring at me. It said all my files had been encrypted and I needed to buy some bitcoin and pay up if I ever wanted to see my data again.
I was not immediately concerned because I had seen threatening web pages like this before. Usually, that’s all they are – web pages designed to scare you into calling a phone number and giving them your credit card info. You simply close the browser or reboot the machine, run a malware scan and they’re gone. Unfortunately, this one was different. It seemed to have my computer in a death grip and persisted after a reboot.
No time to read right now? Download this article in convenient PDF format.
I began searching through my document folders and to my horror I found my files were encrypted. An encrypted file kind of resembles the original file but its filename has been altered with strange characters and extensions. The result is the filenames looked sort of like they have ice crystals forming on them.

Right away I knew what it was – a form of ransomware called “Crypto-locker.” Crypto-locker is quite possibly the worst infection you can get. Your files are encrypted and inaccessible. They can only be unencrypted with an encryption key the hacker claims to have in his possession. Of course, he’ll promise to decrypt your files for you – for a fee.
Contacting the hacker with the email address he provides would be a huge mistake. A mistake that will probably result in him harassing you for the rest of your life because now he knows who you are. If he’s clever enough he can use your email address to get into nearly everything in your digital life.
Never contact a hacker for any reason. That’s what he wants.
A Crypto-locker virus not only destroys files on the computer it’s on but can quickly spread across networks to other machines. It can even spread to USB drives, external hard drives, and unprotected cloud storage drives.
Luckily, the machine I was on was only a test machine I set up to use while writing this eBook. I could easily rebuild it. I poked around on my network and discovered other computers had been infected. What a nightmare! In total 3 of my 5 computers were destroyed including the NAS I used to create Chapter 9 in my eBook. An external USB HD was also destroyed.
The only computers that survived were two I had just installed new antivirus software on the day before! Luckily they were my main computers. Everything else was for testing or backups. So in an odd twist of fate, my backups were destroyed but I still had my original copies.
I also had some cloud storage on Amazon, Google Drive, and Dropbox. Those accounts were all on the machines with the new antivirus so they didn’t get infected either. Thankfully most of my data was intact so it didn’t take long for me to get everything back to normal. Of course, if it weren’t for my cloud backups and the antivirus software I just installed I would have lost everything including the eBook. At the time I had spent nearly 7 months working on it. I would have been devastated.
Malwarebytes 4.5 Latest Version 2022 Antivirus Software | Amazon Exclusive | 18...
In case you’re wondering which antivirus software I installed on the computers that survived it was the trial version of Malwarebytes. I was using some free antivirus software before that. It was not a bad program, but I decided it was time to up my antivirus game a little considering some weird emails, text messages, and even phone calls I was receiving. Amazingly after a lot of research and comparing I ended up not getting Malwarebytes. I got Bitdefender instead. Bitdefender is very comparable to Malwarebytes and I was able to find a nice deal on it.
Bitdefender Total Security 2022 – Complete Antivirus and Internet Security Suite –...
How Could This Happen To Me?
So what happened? How did a guy with over 20 years of experience in the IT field get hacked? In short, I got lazy, overconfident, and let my guard down.
It all started with a phone call. It was a guy with a thick Indian accent claiming to have an American name. I get calls like this all the time from technical recruiters and obvious scammers. I usually hang up on them immediately and block them because I just don’t have the time. In this case, the guy claimed to be from a world-famous shopping website which shall remain nameless. After all, it wasn’t their fault this happened. It was mine. I was intrigued by this particular caller because I had an ongoing issue with a gift card with them and he started asking questions about it. I asked him why I should believe he was legit and he started rattling off details about my gift card balance and account only an actual representative would know – or so I thought.
Next thing I know he’s telling me my account has been hacked and someone was using it to make unauthorized purchases. He told me that two-factor authentication had been set up on my account and I would be receiving an email with instructions on how to reset my password. I got off the phone with him and sure enough, the email arrived. After making sure the email was legit (I’ll describe this later.) I did as instructed. It didn’t work. After several tries, all I got was an error.
I called the 1-800 number on the email (After ensuring it was their actual customer service number.) They put me through a security protocol the first guy didn’t. That should have set off a red flag but, I was too focused on getting the whole ordeal over with so I pushed on. They were able to walk me through changing my password and getting me back into my account. I believe it was at this point that the guy captured my password. I still don’t know how he was able to trigger the internal email though. The second account representative I spoke with knew nothing about the first guy. It was at that point I realized I’d been bamboozled.

Someone on the other side of the world now had access to all the credit cards, bank accounts, devices, movies, and music I had with that account. I immediately removed all my methods of payment and put a super long, super complex password on that account. I called the company again and they said they would file an “unauthorized activity” report. They also suspended my account for investigation. The bad guy only got away with my gift card balance which would soon be replenished.
I thought I won.
The rest of the story is what nightmares are made of. The very next day I realized my personal computers were encrypted and destroyed. I had to rebuild them and redo my entire network. I ended up canceling all my credit cards, and bank cards, and changing all my important online account passwords to extremely long and complex passwords. I destroyed all my plastic and spent the next week or so living in “cash only” mode for weeks until new cards were issued.
I don’t know for sure if it was the same guy but it certainly seemed like he became frustrated with the small amount of money he got from me so he sent me the Crypto-Locker virus as a “parting gift” and a last-ditch effort to make me a lucrative victim.
The first thing I had to do was assess the damage.
I unplugged my modem and turned off my wireless router. I would not be back online again for a full week. I needed to go over each machine with a fine-tooth comb. Two systems were Linux machines that supposedly don’t get infected. One of those was my NAS. I cringed as I realized some of my most precious memories were gone. The second computer was an Ubuntu NAS built on a cheap old computer. It was mostly used for backups. Everything on it was gone also.

The third one was the PC the threatening webpage appeared on. I initially installed a free antivirus program on that one because it was just a test machine. It worked great for a while but now it was toast as well. An external hard drive I had attached to my wireless router for file-sharing was also completely encrypted. That hurt.
Disaster Recovery
I needed to start somewhere so I immediately pulled out an Operating System CD, formatted the hard drive, and began the computer rebuild process on the test machine. I would need it to test network connections to my other computers. I completely formatted the drive, installed a new operating system, installed a basic set of programs, updated it, and installed the new antivirus – of course!
The two computers that survived were Windows 10 computers with the new Malewarebytes software installed. These were my most important computers. Thank God! They were the reason the Ubuntu backup server existed. I was grateful the files on both were still intact but I needed to make sure the Operating Systems were clean so they could not infect other computers on the network and start the whole cycle over again.
I knew Malewarbytes had just been updated with the latest virus definitions so I used it to do deep scans on my remaining computers with my fingers crossed. Miraculously they came up clean. I formatted a USB drive and inserted it into the two machines as a test. I waited and scanned the USB drive to see if it became infected. It didn’t. Next, I networked them with my test machine using ethernet cables and a switch. I did a scan on all three computers and everything was clean. Suddenly there was a glimmer of light at the end of the tunnel.
At this point, I had three good computers up and running but I still refused to connect them to the Internet. Somehow a 1TB external hard drive attached to the wireless router became infected so there was no way of telling how safe an Internet connection would be at this point. I needed a reliable way to restore my most important computers if the bad guys got back into my home network.
For my peace of mind, I formatted the external USB hard drive, connected it to each of my good Windows computers, and ran an awesome Windows utility which is kind of hidden away in the Backups section. It’s called System Image Backup.
You’ll find it under Settings/Update and Security/Backup/Backup And Restore. Another window opens. The letters are so tiny it’s easy to miss but if you look at the bottom left corner of the window there it is – “System Image Backup.”
The problem with a normal backup of your files is if your computer’s hard drive crashes and needs to be replaced or if it needs to be completely formatted you have to start from scratch. That means you have to install the Operating System, update it, install your devices, install your printers, reinstall all your programs, and recreate your accounts before restoring your files. It can take several days. Some people never get their computers back to the way they used to be. System Image Backup offers an alternative.
A system image is like a snapshot of your computer. It’s a copy of everything on your computer at a given moment. The Operating System, the updates, drivers, accounts, and programs are all copied and frozen in time to a “System Image.” I recommend doing this overnight once a month because it can take a few hours. I also recommend doing this in addition to regular file backups.

- Click on “Create a system image” to begin the process.

- Select the external hard drive you want to copy your System Image to.
- If you want to you can span multiple DVDs. This is not recommended.
- You can also save your system image to a network location. I would only do this on a fast and reliable network.
- Click “Next” to get the process started. I would do this overnight because it can take a few hours. You don’t want to use your system while it’s running.

You’ll be given the option to create a System Repair Disc. If your computer has a CD/DVD drive I highly recommended you do this. If not I recommend you use a USB stick to create a Recovery Drive. I describe how to do that at the end of this section.

Both the System Repair Disc and the Recovery Drive are designed to work with the System Image you created. You can use it either to boot your computer, format your hard drive or install the System Image Backup.
Insert your recovery tools (Repair Disc or Recovery Drive) and restart your computer. When the computer restarts immediately start tapping the key your computer uses to bring up the boot menu.
Acer, Dell, Lenovo = F12
Asus = Esc
HP = Esc then F9
Samsung = Esc or F10
You have to be quick. It may take a few tries to get it right.

- Use the up and down keys to select either the DVD or USB drive with your recovery tools and hit Enter.
Note: If your Operating System is still working there’s a much easier way to do this from within Windows. Simply go to Settings/Update & Security /Recovery/Advanced Startup and click on the “Restart Now” button. Your system will reboot to the same Advanced Startup Options screen.

- From Settings go to “Recovery.”
- Under “Advanced Startup” click on “Restart now.”
Whether you use the USB Recovery Drive, DVD System Repair Disc, or the Windows Recovery option your computer should reboot to the Advanced Startup Options Screen below. Here you’ll find multiple repair options including a System Image Recovery utility you can use to restore your computer from the System Image you created.

- When the Select “Troubleshoot.”
- Select “Advanced options.”
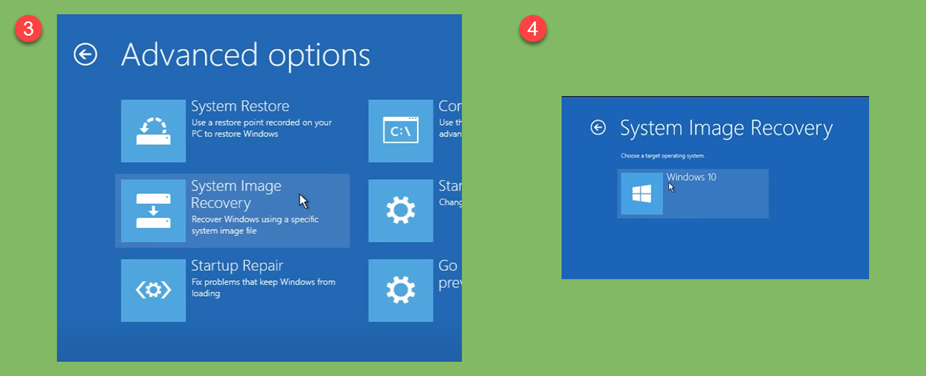
- Select “System Image Recovery.”
- Select the Operating System you want to recover.

- The utility will search your external hard drive for the System Image you created. Click “Next” to begin the process. In a few hours, your system should be returned to the same state it was in when you created the image!
I consider System Images to be my most important recovery tool. I can have a system back up and running in a matter of hours and the external hard drive can be taken to a location outside my home for safekeeping.
Note: File backups and system images are not a fascinating topic for most, but the fact is hard drives crash. This is the type of skill you want to master sooner than later. There is an excellent free program called Macrium Reflect that is more intuitive and full-featured than Microsofts recovery programs. I highly recommend looking into it.
Some things to keep in mind when creating a System Image Backup:
- The external hard drive you use needs to be the same size or greater than the hard drive you’re imaging.
- If you replace the hard drive in your computer the new hard drive needs to be the same size or greater than the original hard drive.
- A System Image only works on the computer it was created from. If your entire computer dies you can’t use the System Image from that computer on another computer.
Note: If you go through all the trouble of saving a System Image to an external hard drive please make sure you disconnect it to make sure it doesn’t get infected along with your system if it happens again.
I mentioned earlier I would demonstrate how to make a Windows 10 Recovery Drive on a USB stick. It’s amazingly simple. First, insert a USB stick that has at least 16GB into your computer.

- From within Control Panel (Enter control into the search bar.) go to “Recovery.”

- Click on “Create a recovery drive.”
- Make sure “Back up system files to the recovery drive” is checked.
- Click “Next” to start the process. It should take about an hour.
The USB Recovery Drive serves the same purpose as DVD System Repair Disc. Once you get to your computer’s boot menu simply select USB device instead of CD/DVD drive.
OK, now where was I? Oh yeah…I was in the process of carefully bringing my network back up one computer at a time. I was at the point where I had three clean computers up and running. Before I risked another round of infections by connecting them all to the Internet I created a System Image for each one using the Microsoft tools described above. I saved them all to an external hard drive. This can also be done with an excellent free program called Macrium Reflect. I highly recommend it.
At this point, I honestly didn’t know if I was dealing with a random infection or a deliberate attack on my network. If it was a deliberate attack I would be leaving myself vulnerable by using the same Internet IP address. If that was the case my wireless router had to go. Fortunately, being the “Wi-Fi-Guy” there’s no shortage of wireless routers at my place.
Most ISPs use a router’s external MAC address to assign it an external DHCP IP address. It works the same way as on our internal network. So I theorized that if I replace my wireless router with one with a different external MAC address I should end up with a different external IP address. It worked. I now had what amounted to a new identity on the Internet. I was feeling more and more confident about going back online.

- Under “Basic” and “Internet” I was able to verify my new wireless router’s new external IP address.
You can also try a neat trick called MAC address cloning to get a new IP address.

- In your wireless router’s Internet or WAN section, you should be able to get your wireless router to “clone” your local computer’s MAC address to its external network interface. If all goes well the new MAC address will result in a new IP address.
I spent the next few days connecting each of my computers to my new Internet connection one by one and carefully monitoring them for signs of infection. Once I was confident they could each survive exposure to the Internet I put them all online simultaneously. I’m convinced if I didn’t use such a disciplined approach to putting them back online I could have ended up with a worse disaster. Attempting it with no image backups to fall back on would have been just asking for trouble.
Once I had my two main computers and one test machine up and running I completed the setup of my new wireless router complete with new SSIDs and Wi-Fi passwords. I then began the sad task of blowing away both my NAS servers and rebuilding them. I did this by removing both hard drives and formatting them to avoid putting them back on the network.
Fortunately, I had most of my music, pictures, and movies saved in cloud storage so it wasn’t a total loss.
What Went Wrong And How I Fixed It
So how did I leave myself open to this?
- I made the mistake of interacting with a hacker.
- I became lackadaisical in my approach to Internet security.
- I got lazy with passwords. I was using the same password on several accounts.
- I was using my browser to save passwords.
- I didn’t have updated antivirus software on all my computers.
Could it have been worse? Yes, it could have been way worse if I:
- Had no antivirus installed at all.
- Had no backups.
- Immediately put all my computers back online in a rushed or haphazard manner.
How did I recover?
- I immediately disconnected from the Internet.
- I scanned all my computers for infections.
- I immediately removed the infected computers from the network and did not reconnect them until they were reformatted.
- I made image backups of all my good computers.
- I used a disciplined approach to bring my computers back online.
- I temporarily disabled all my financial accounts.
What have I done to make sure it never happens again?
- Changed all my online account passwords to extremely long, complex passwords.
- I never save passwords in my browser anymore. I use a password manager to remember them for me.
- I created a text file with my new, complex passwords, and keep it in a secure location.
- I had my credit card companies reissue new cards for me.
- I opened a separate bank account for online ordering and only transfer money to it on an as-needed basis. This prevents someone from draining all my accounts.
- I use reputable antivirus software on ALL my computers.
- I keep all my software and Operating Systems up to date. As soon as an update becomes available, I run it.
- In addition to file backups, I maintain system image backups off all my important computers. If a computer crashes or becomes unusable I can usually be back up and running in a matter of hours.
Here’s a nice site to help you with long, complex passwords – passwordsgenerator.net

To avoid having to type in passwords that look like “G&8J)XLZgH,]$q5A” you can use a password manager program like LastPass or Bitwarden to generate, store and enter your complex passwords for you. LastPass has a browser plug-in that notices when you create a password for a new site and asks if you want to save it in your vault. When you want to access that site later it’s a simple matter of launching that site from your LastPass account.
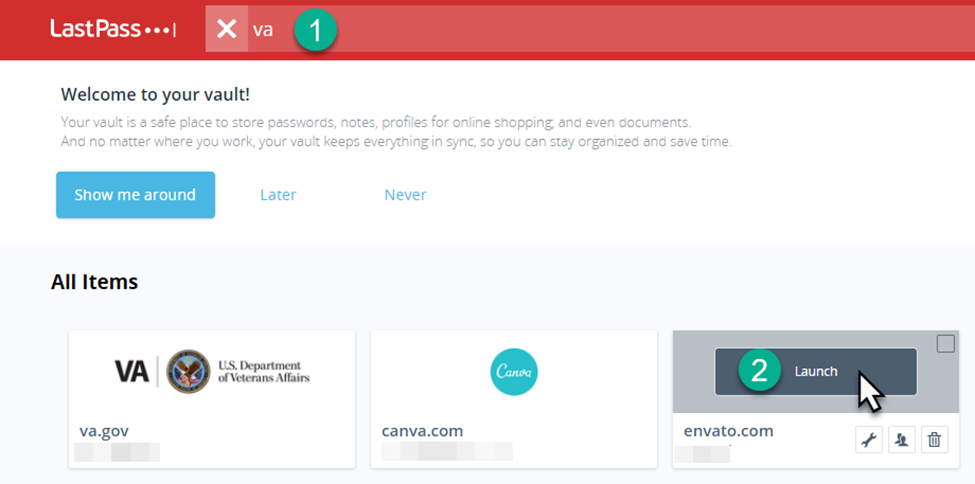
- Do a simple search for your website.
- Click “Launch” to open the site and enter your login credentials automatically.


















I’m a loyal user of the same pass generator tool. Unfortunately it’s been down for a few months now but it looks like it’s reachable again at https://password-gen.com